OxideTerm
Zero Electron. Zero OpenSSL. Zero Telemetry. Zero Subscription. BYOK-first. Pure Rust SSH.
A local-first SSH workspace: open a remote node once, then work around it with shell, SFTP, port forwarding, trzsz, lightweight editing, local shell, and BYOK-first OxideSens AI.
THE DIFFERENCE
Why OxideTerm?
Not just a terminal. A remote-node workspace that stays local-first.
| The Problem | OxideTerm's Answer |
|---|---|
| SSH workspace, not just a shell | Remote node workspace — terminals, SFTP, port forwarding, trzsz, lightweight IDE, monitoring, and AI context under one node |
| You still need a local shell | Integrated local shell — zsh/bash/fish/pwsh/WSL2 beside SSH sessions, so local and remote tasks share one UI |
| Remote file editing needs VS Code Remote | Built-in IDE — CodeMirror 6 over SFTP with 24 languages, optional ~1 MB remote agent |
| No SSH connection reuse | Multiplexing — one SSH connection shared across terminal, SFTP, forwarding, and IDE |
| SSH libraries depend on OpenSSL | russh 0.59 — pure Rust SSH compiled against ring. Zero C dependencies |
| 100+ MB Electron apps | Tauri 2.0 — 25–40 MB binary. Not a wrapper — genuine native app with Rust backend |
| You do not want telemetry or app subscriptions | Zero tracking, zero core app subscription — SSH/SFTP/port forwarding/local shell need no OxideTerm account or subscription; Cloud Sync is opt-in via plugin |
| Credentials stored in plain-text configs | Encrypted at rest — OS keychain for passwords, ChaCha20-Poly1305 + Argon2id for .oxide exports. Nothing in plain text |
| You want AI without a platform account | BYOK-first OxideSens — target-first workspace AI for saved connections, live SSH sessions, terminal buffers, SFTP paths, settings, and knowledge base entries |
LIVE DEMO
Watch It in Action
OxideSens AI can control live terminals and workspace tools from one assistant.
DEEP DIVE
Everything You Need, Nothing You Don't
Terminal
- Split panes with broadcast input to all sessions
- WebGL rendering at 60fps+ with 120Hz burst mode
- Session recording & playback (asciicast v2)
- 31+ themes with a full CSS variable custom theme editor
- Command palette (⌘K) and zen mode
- Configurable keyboard shortcuts with vi-mode support
- Auto-complete for SSH hostnames and saved sessions
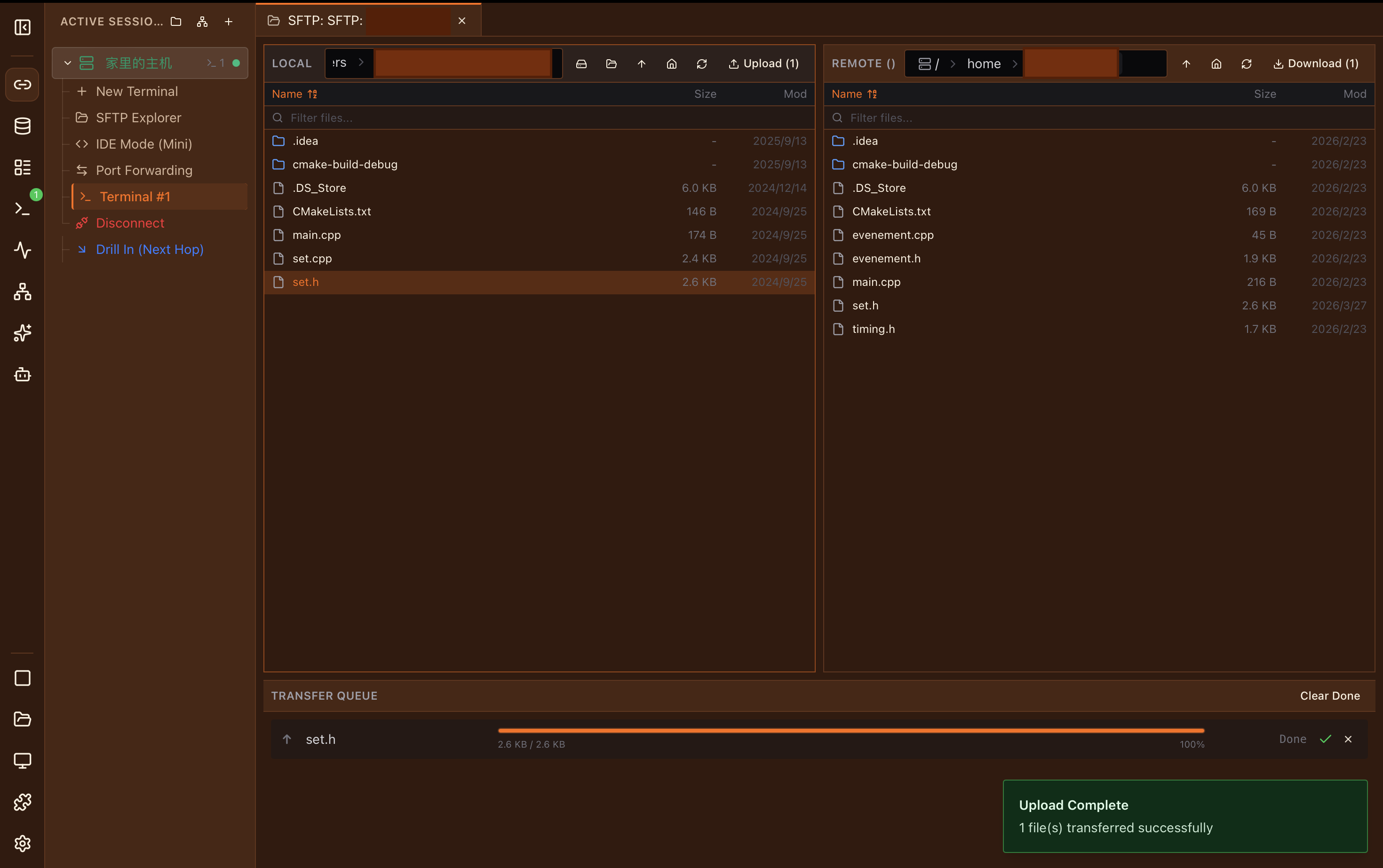
SFTP File Manager
- Dual-pane browser with drag-and-drop
- Smart preview: images, video, audio, code, PDF, hex, fonts
- Transfer queue with real-time progress & ETA
- Bookmarks and archive extraction
- Rename, delete, create folders, and batch transfers
- Watch mode with auto-upload on local changes
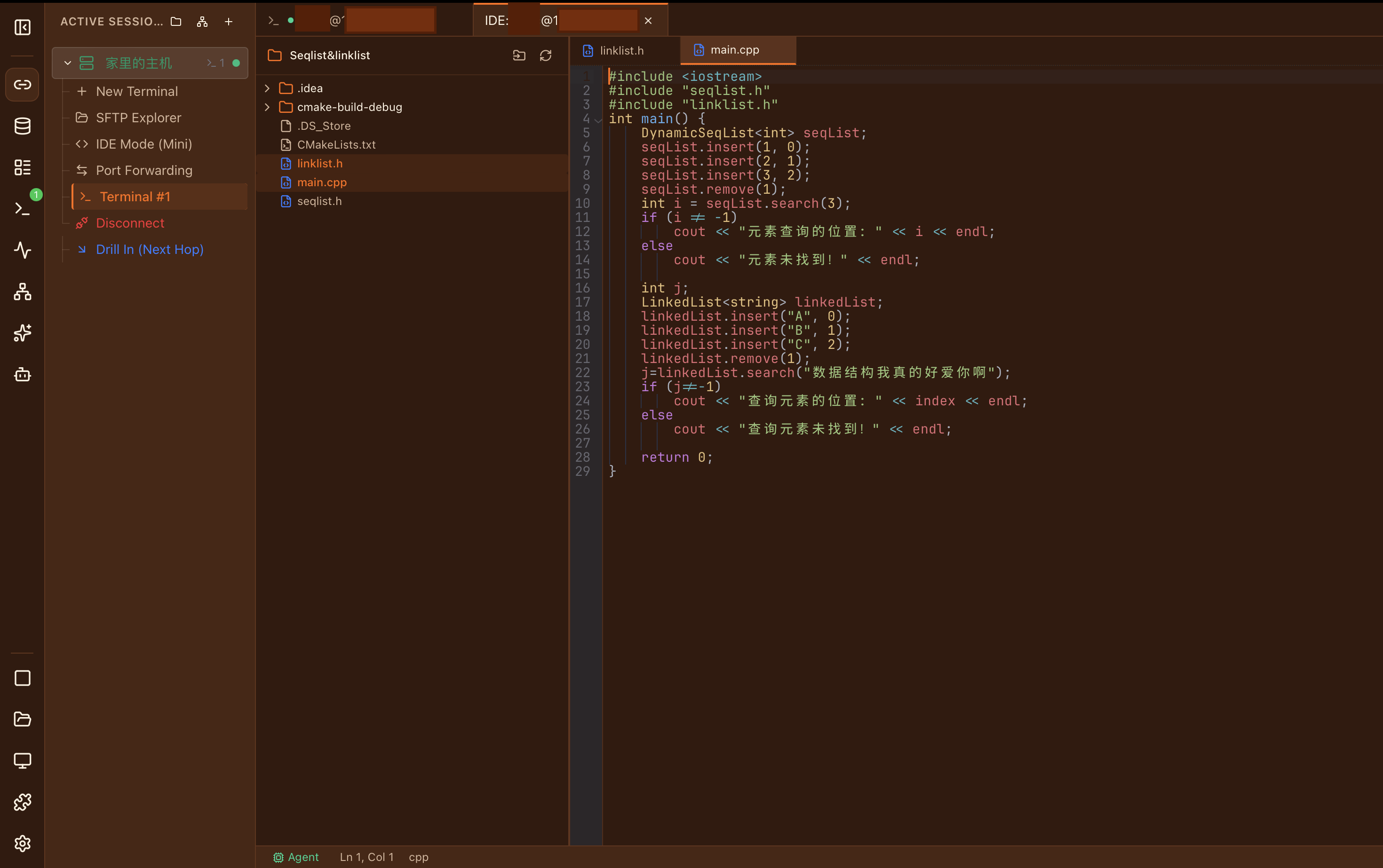
Built-in IDE
- CodeMirror 6 with 24 language modes
- File tree with Git status indicators
- Multi-tab editing with conflict resolution
- Optional ~1 MB remote agent (Linux, 9 architectures)
- Search & replace with regex across remote files
- Syntax highlighting for 24 languages: Rust, Python, JS/TS, Go, C/C++, Java, YAML, JSON, TOML, Markdown, Shell, and more
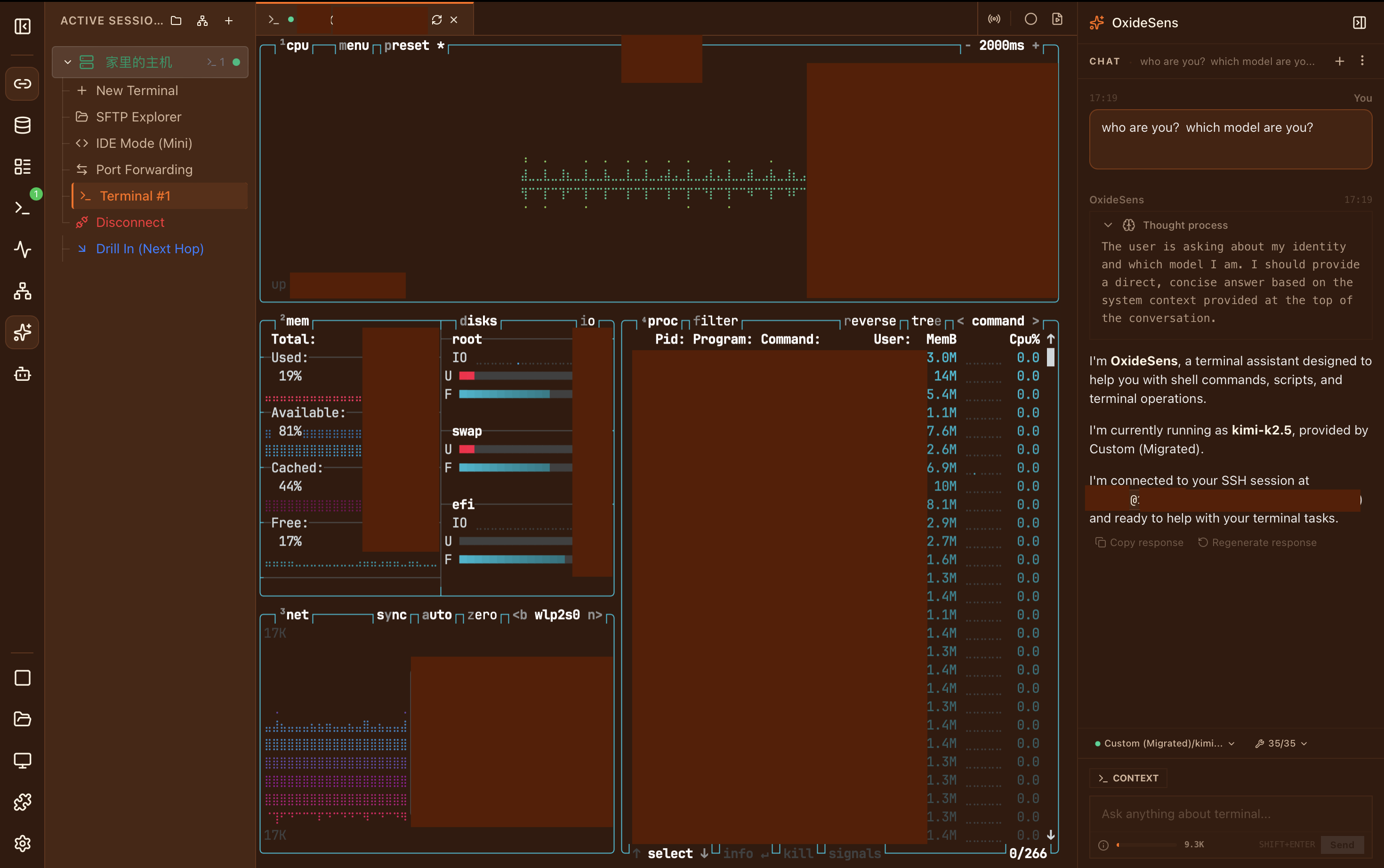
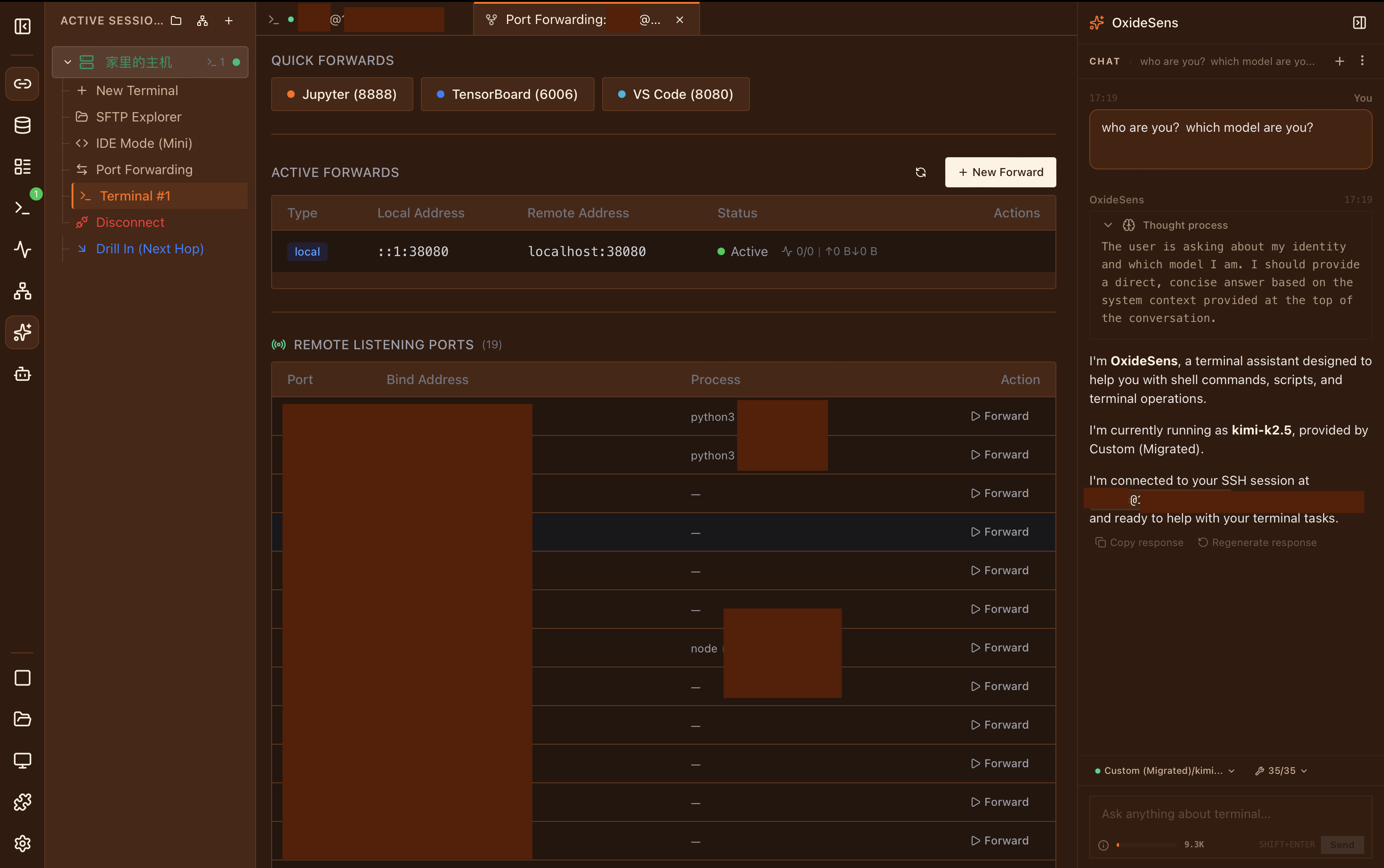
OxideSens AI
- Inline panel (⌘I) + sidebar chat
- Target-first workspace tools, not a giant tool list
- RAG knowledge base with keyword + vector retrieval
- Diagnose remote output, run approved commands, inspect files, and explain failures
- Bring your own key — OpenAI, Anthropic, Google, DeepSeek, Ollama, or compatible endpoints
Port Forwarding
- Local (-L), Remote (-R), Dynamic SOCKS5 (-D)
- Lock-free message-passing I/O
- Auto-restore all forwards on reconnect
- Death reporting and idle timeout
- Real-time bandwidth and latency monitoring
ZERO TRUST
Security First
Enterprise-grade protection without enterprise complexity.
High-Strength Encryption
ChaCha20-Poly1305 AEAD with Argon2id KDF (256 MB memory, 4 iterations) for .oxide encrypted exports.
OS Keychain Integration
Passwords and API keys stored in macOS Keychain, Windows Credential Manager, or Linux Secret Service. Never in config files.
Pure Rust Cryptography
russh 0.59 with ring crypto backend. Ed25519, RSA, ECDSA keys. ChaCha20-Poly1305 and AES-GCM cipher suites.
Biometric & TOFU
Touch ID gates keychain access on macOS. Host key verification with Trust-On-First-Use (TOFU). Sensitive memory zeroized on drop.
Memory Zeroization
All sensitive data — passwords, keys, decrypted payloads — is securely erased from memory via the zeroize crate. Drop handlers guarantee no lingering secrets.
Single-Use WS Tokens
Each WebSocket bridge receives a unique, single-use token with a time limit. Prevents replay attacks and unauthorized session hijacking.
ARCHITECTURE
Under the Hood
Dual-Plane Architecture
WebSocket binary frames for terminal I/O, Tauri IPC for control commands. Each session gets dedicated bandwidth.
WebGL Rendering
GPU-accelerated terminal via xterm.js 6. Adaptive scheduler: 120Hz+ burst, 60Hz normal, 1–15Hz idle backoff.
Connection Multiplexing
One SSH connection shared across terminal, SFTP, forwarding, and IDE. Reference-counted pool with automatic cleanup.
High-Strength Encryption
ChaCha20-Poly1305 AEAD with Argon2id KDF (256 MB memory, 4 iterations). OS keychain for passwords, Touch ID gate on macOS.
11 Languages
Full UI translation across 22 namespaces: English, 简体中文, 繁體中文, 日本語, 한국어, Français, Deutsch, Español, Italiano, Português, Tiếng Việt.
Plugin Ecosystem
Runtime ESM plugins with 18 API namespaces, a built-in UI kit, and native tabs, sidebar panels, context menus, status bar items, shortcuts, and progress UI.
FROM THE CREATOR
I built OxideTerm because I wanted one tool that actually does everything — SSH, SFTP, port forwarding, code editing — without feeling heavy or asking for a subscription. The tech choices (pure-Rust SSH, binary wire protocol, ChaCha20 encryption) aren't there to show off; they're just what made sense when you want something fast, portable, and correct. It's a solo project, so it won't be perfect, but I'd rather ship something honest than something polished with corners cut.
COMPARE
How Does OxideTerm Compare?
A factual look at what different approaches to terminal tooling offer.
| Capability | OxideTerm | Electron-based | Traditional |
|---|---|---|---|
| Binary Size | 25–40 MB | 100+ MB | Varies |
| SSH Implementation | Pure Rust (ring crypto, zero C deps) | Typically OpenSSL / libssh2 | System SSL or built-in |
| Local Terminal | ✓ | Partial | — |
| Built-in SFTP | ✓ | Partial | Partial |
| Remote Code Editing | ✓ | — | — |
| AI with Terminal Context | ✓ | — | — |
| Graceful Reconnect (Session Preservation) | ✓ | — | — |
| Connection Multiplexing | ✓ | — | Partial |
| Plugin System | ✓ | — | Partial |
| Multi-language UI | ✓ | Partial | Partial |
| Open Source | ✓ | Varies | — |
| Free to Use | ✓ | Varies | Varies |
Comparison reflects general category trends, not any specific product. Individual tools within each category may differ.
COMMAND LINE
CLI Companion
Meet oxt — your terminal wingman.
JSON-RPC 2.0 over Unix Socket (macOS/Linux) or Named Pipe (Windows). Human-friendly and machine-parseable output.
FAQ
Frequently Asked Questions
Is OxideTerm free?
Which SSH authentication methods are supported?
Where is my data stored?
Can I use OxideTerm offline?
What do I need for AI features?
Why doesn't OxideTerm use libssh2 or OpenSSL?
COMPLIANCE
Compliance & Legal
OxideTerm is designed for legitimate system administration, development, and research. We take compliance seriously.
Network Compliance
OxideTerm is a professional remote server management and terminal emulation tool. This software is intended solely for compliant system administration, network management, software development, and academic research. Users must strictly comply with all applicable laws and regulations when using SSH tunneling or port forwarding features. Any use of this software for unauthorized access to restricted resources or violation of cybersecurity regulations is strictly prohibited.
AI Service Disclaimer
The AI-assisted features provided by OxideTerm (such as command completion and log analysis) function as technical integration tools. AI conversation history is stored locally on the user's device using encrypted storage and is never uploaded to any server. The software does not distribute AI-generated content to third parties. Users are responsible for configuring their own third-party AI service API credentials and bear ultimate legal responsibility for the resulting interactions. We recommend using these features in compliance with all applicable AI governance regulations in your jurisdiction.
Data Security & Privacy
We understand the sensitivity of operational data. OxideTerm adopts a Local-First architecture. All server credentials, keys, and configuration files are encrypted and stored exclusively on the user's local device using high-strength encryption algorithms. This software does not collect, upload, or disclose any sensitive connection data to third parties.
License
This software is distributed under the GNU General Public License v3.0 (GPL-3.0). OxideTerm previously used PolyForm Noncommercial and moved to GPL-3.0 to avoid source-available traps, noncommercial ambiguity, and no-competition riders. Public code is not automatically open source: no-redistribution, no-repackaging, no-competing-products, or platform-approval riders turn it into source-available branding. OxideTerm adds none of those riders.
This page is provided for informational purposes only and does not constitute legal advice. Users are responsible for ensuring their use of OxideTerm complies with all applicable local and international laws.
GET STARTED
Download OxideTerm
Available for macOS, Windows, and Linux
Requires macOS 10.15+, Windows 10+, or Linux (glibc 2.31+). Uses the system WebView runtime; most systems already include it.
View all releases on GitHub →